


It might have snuck up on us over the last few years, but today the concept of storing files in the cloud is an indispensable part of our working life. Data saved in the cloud, however, is not necessarily safe. Just like with files saved to our computers, data stored in the cloud can be leaked or stolen.
Using encryption for data saved to the cloud can provide assurance that none of our sensitive information will be read by third parties.
Here we’ll discuss the importance of encrypting data in the cloud and review some different encryption options. Finally, we’ll talk you through our best practices for companies that want to build a cloud encryption strategy.
One reason why cloud encryption should be essential for companies is due to frequent data breaches on cloud services. According to a new survey conducted by Ermetic, 79% of participating companies said they had experienced at least one cloud data breach in the last 18 months.

If you don’t use encryption to protect the data you save in the cloud, then your information is only protected by an online key. These online keys are the individual passwords that you enter in order to access your cloud account. Cloud providers store your online keys. If your cloud provider is hacked, your data will become accessible.
By hacking the server of one cloud provider, attackers can access the unencrypted data of millions of people and companies.
The best way to ensure your cloud data remains safe is to encrypt your files. When data is encrypted before being uploaded to the cloud, you add an extra layer of privacy protection to your account – making data breaches much less likely. So even if your online account gets exposed, your encrypted files could still only be seen by entering the correct key, which cyber criminals would not possess – only you hold your own encryption keys.
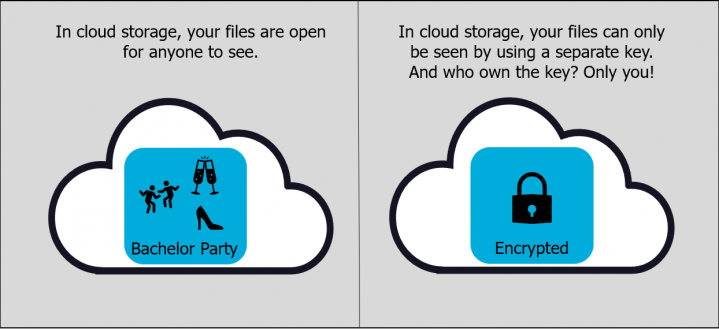
When we talk about encryption keys, we’re referring to codes used by organizations or users to access and unscramble their encrypted files. Essentially, the keys are what will let you access your data, while making sure to block out prying eyes.
Considering the importance of encryption keys, it only makes sense that we discuss who manages them. Companies must ask themselves if they prefer the idea of paying extra fees to let cloud services manage their keys, or if they want to manage their encryption keys themselves.
How can you add an encryption key to your existing online account? There are 2 ways to go:
Now that you have a better idea about your choices when it comes to cloud encryption, let’s go through some best practices for putting together a cloud encryption strategy for your company.
Now you’re on your way to put together your own encryption strategy for data saved in the cloud. If you’d like some more information on data encryption solutions for enterprises then be sure to check out this simple guide.
Happy Encrypting!
Looking for an alternative to Boxcryptor? Read 3 reasons why you should choose BestCrypt.

Michael Waksman has been serving as CEO of Jetico since 2011, more than doubling the size of the company during his tenure. He brings more than 20 years of communications, technology and leadership experience.
At Jetico, Waksman has lead creation of the corporate identity, raising global brand awareness, building a more commercially-driven team and initiating enterprise customer relations. Jetico has maintained a wide user base throughout the U.S. Defense community, in the global compliance market and for personal privacy.
Waksman served as vice-chairman of the Cyber Group for the Association of Finnish Defense and Aerospace Industries. Recognized as a security and privacy advocate, he is a frequent speaker at international events, occasionally on behalf of the Finnish cyber security industry. In 2012, Waksman was honored with The Security Network's Chairman's Award for fostering collaboration between the United States and Finland. As dual citizen, he is a native New Yorker and has been living in the Helsinki region for over 15 years.
