


In this video you will find detailed instructions on how to gain added security by using Password Based Encryption in BestCrypt Container Encryption.
Keyfiles allow users to add another level of authentication on top of standard password protection - a much beloved and missed feature of now-defunct TrueCrypt. To learn how to use Keyfiles, watch the video.
Download BestCrypt Container Encryption
Learn more about BestCrypt Container Encryption
In this video tutorial, we’ll show you how to gain added security by using the Password Based Encryption method with Key files and Key Stretching techniques.
Open BestCrypt Control Panel. Click 'Container Menu' and select 'New'.
Select the container file path. Then select the size and provide a brief description. Now go ahead and click 'Create'.
Instead of entering the password, click 'Show Advanced Settings'.
BestCrypt provides you with 3 different Encryption Schemes. Here we will select ‘Password Based Encryption’.
For the hash algorithm – we will select SHA-512 – the salt size would be automatically adjusted per the hash algorithm – the number of iterations by default is 16384, but you can edit this number. Just remember that a higher number of iterations makes it harder for a brute force or dictionary attack. This is also called the mount benchmark, since it also determines mounting time for this container, this time is also mentioned next to the iteration box. (Here we will keep the standard number.)
Key Files allow you to add another layer of authentication on top of standard password protection, increasing the resistance of your container against brute force attacks. This method is a form of two factor authentication.
To enable this feature, click 'Key File' and select a file. Then, remember to secure this file for future authentication. Without this file, you will not be able to access your container.
You can create backward compatible containers by checking 'v.8 and cross platform compatible'. If you choose this option, you will be prompted to remove the Key Files function which will not work in older versions of BestCrypt, also the hash will be restricted to SHA256 with 256 iterations. Click 'Yes' if you are creating a version 8 compatible container. We will Click 'No' for the latest version container.
By checking the ‘Encrypt Header’ box, you can encrypt the container header to disguise encrypted files as random data. If you change the container file extension and encrypt the header, the container cannot be reliably distinguished from a regular file which will enhance your privacy. BestCrypt will attempt each algorithm until it succeeds to authenticate your container.
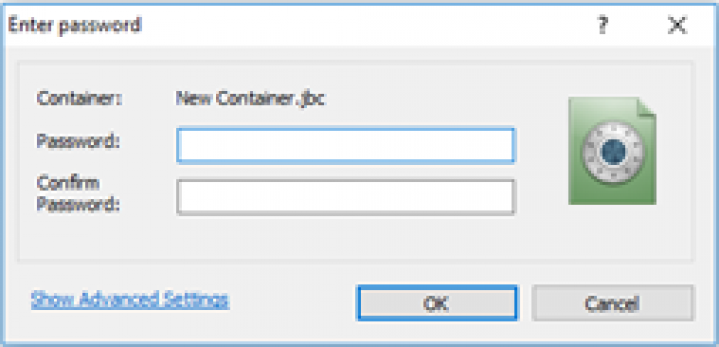
Choose a password for the new container and click 'OK'.
Move your mouse around this window or type anywhere on the keyboard to generate random data for the encryption key.
Format your container. Dismount it.
Let’s now try to mount the container by using your Key File. Right-click on the container and select mount.
Click ‘Show Advanced Settings’, click ‘Key Files’ and select the authentication file.
Enter your password and click 'OK'.
CONGRATULATIONS! You have successfully created a container with added security by using Key files and Key Stretching techniques. Thank you for watching! We hope you will be satisfied with our software.
