Quick Start
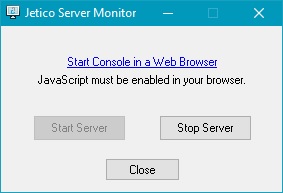
This Quick Start guide assumes that the server has been installed and the hyperlink on Jetico Server Monitor window is available (see image below).
For information pertaining to the JCM server installation, proceed to the Jetico Central Manager Installation portion of this manual.
Click the hyperlink to open the JCM Console in the default web browser.
Alternatively, the JCM Console can be accessed in the following ways:
- using the link https://*.*.*.*:8443 (where *.*.*.* is the IP address of the JCM server computer)
- if the server was installed on the same computer where JCM Console is open, use the link https://localhost:8443
The following steps will encrypt your company's computers with default settings:
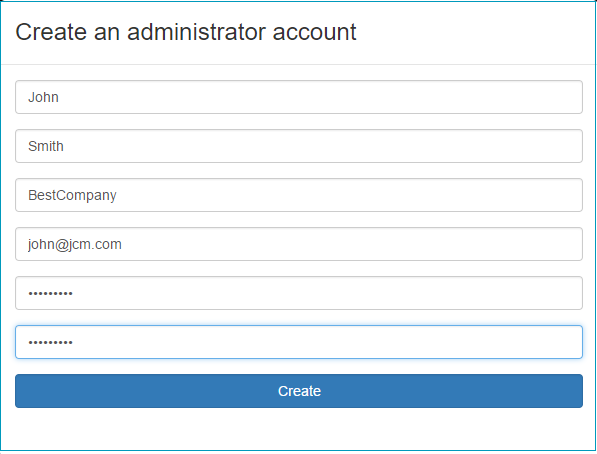
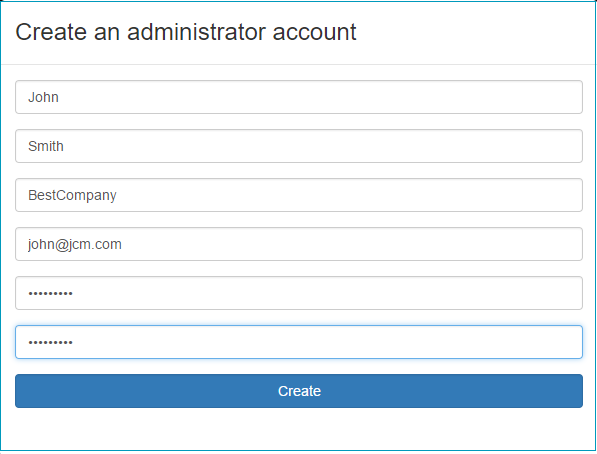
- Create an administrator account and log in to the Console. When JCM Console is opened for the first time, the program will ask you to create the first administrator account by typing the user name, company name, email address and password:
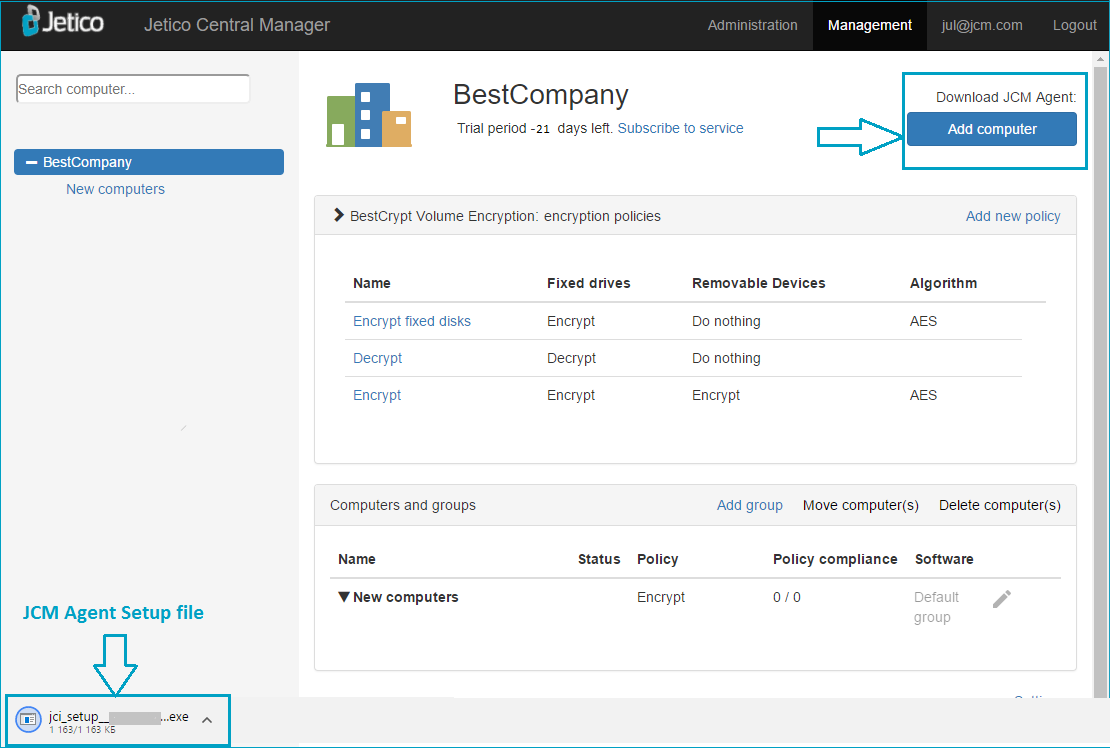
As soon as the account is created and you logged in, JCM Console appears and looks like:
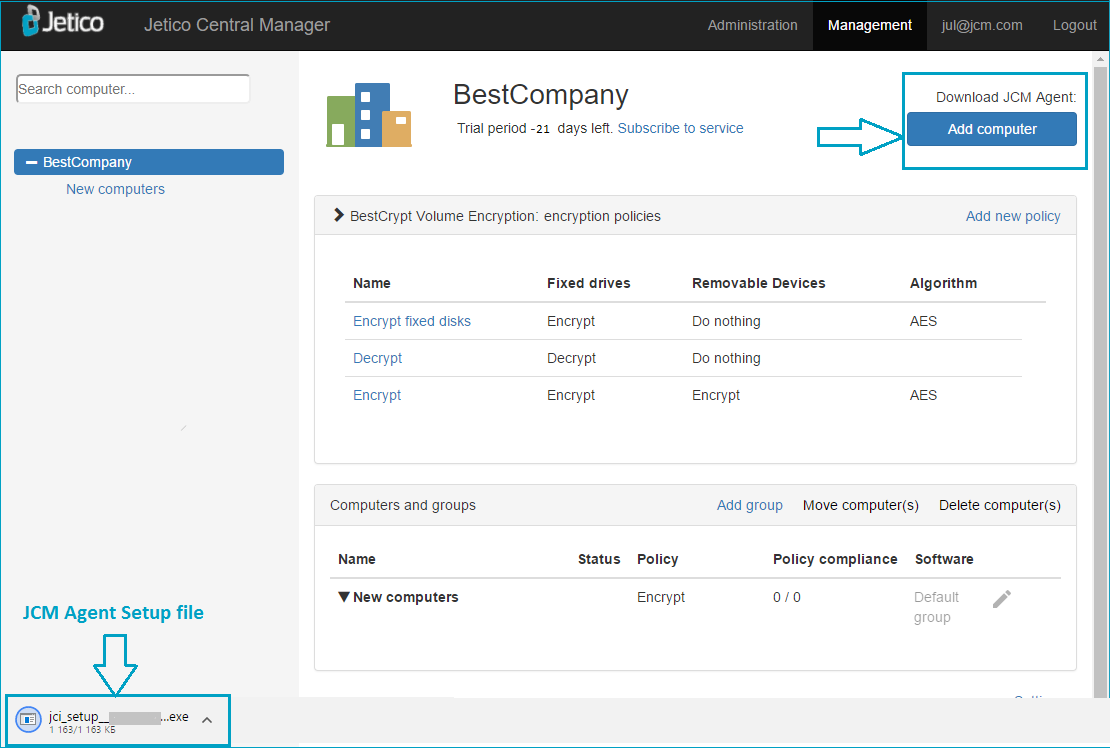
- Create JCM Agent Setup file. Now click Add computer and see in the bottom part of the browser that the JCM Agent Setup file is downloaded.
Copy this Setup file to a network shared location, or to a USB stick.
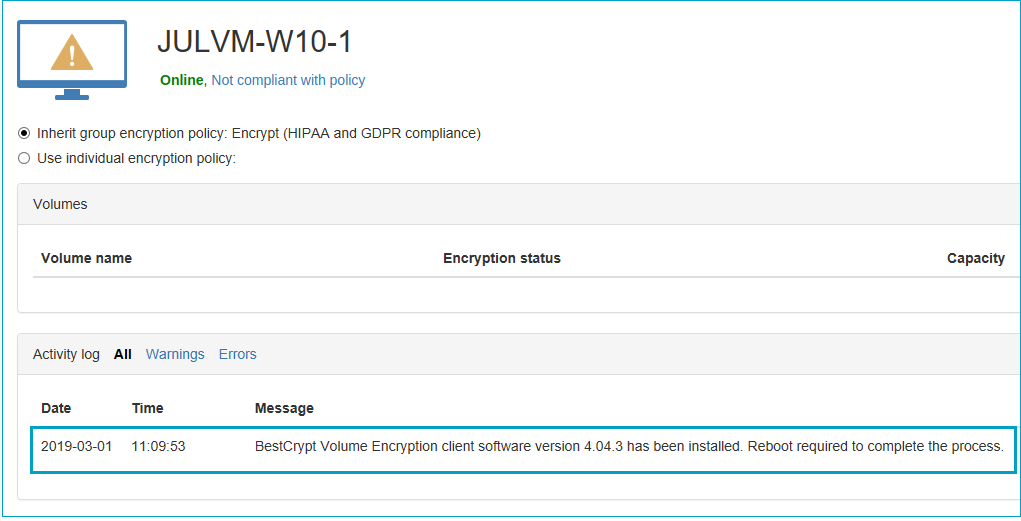
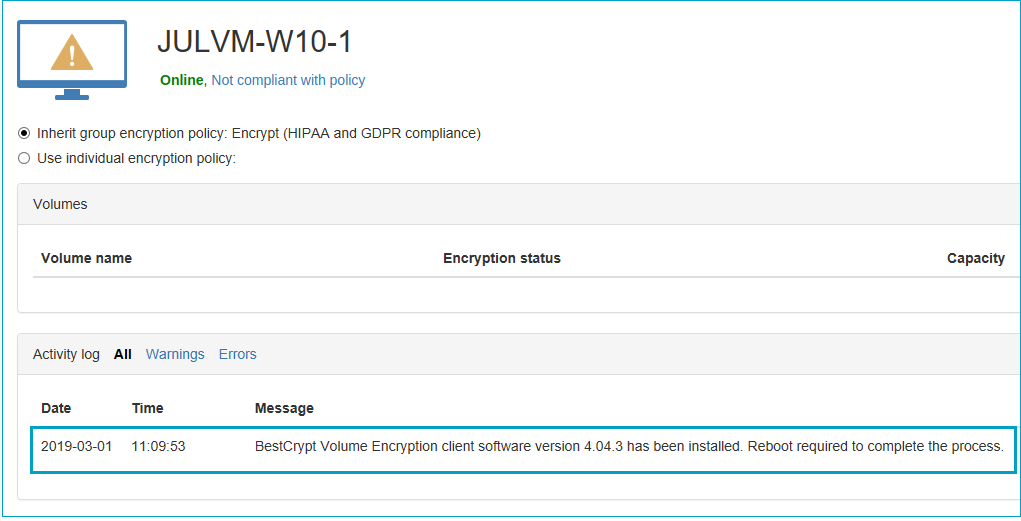
- Add client computer. Run the Setup file on a computer that should be encrypted (client computer). The Setup program will be running silently. After installation of the JCM agent,
JCM Console will show the computer added to database. Agent will connect to the server and install the client software automatically. After installation of the client software, the log message
will be sent to the computer page of JCM console:
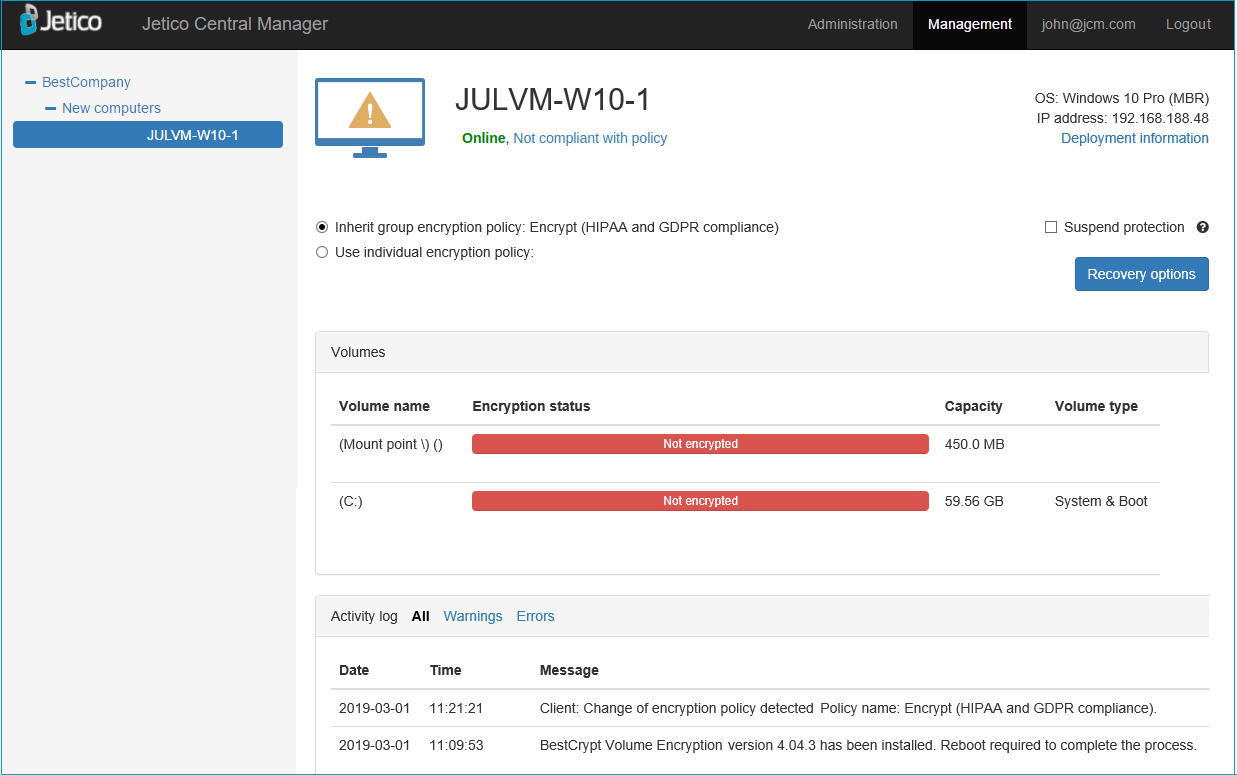
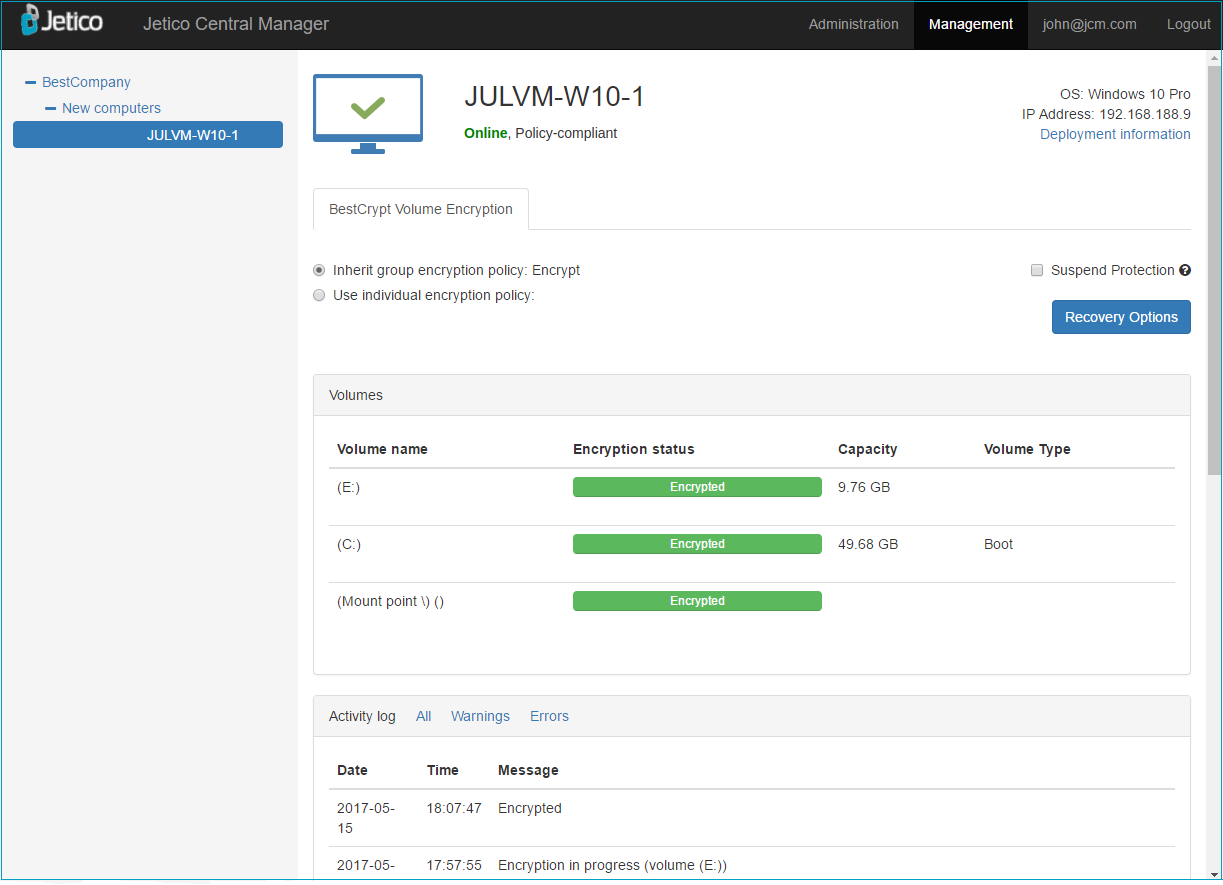
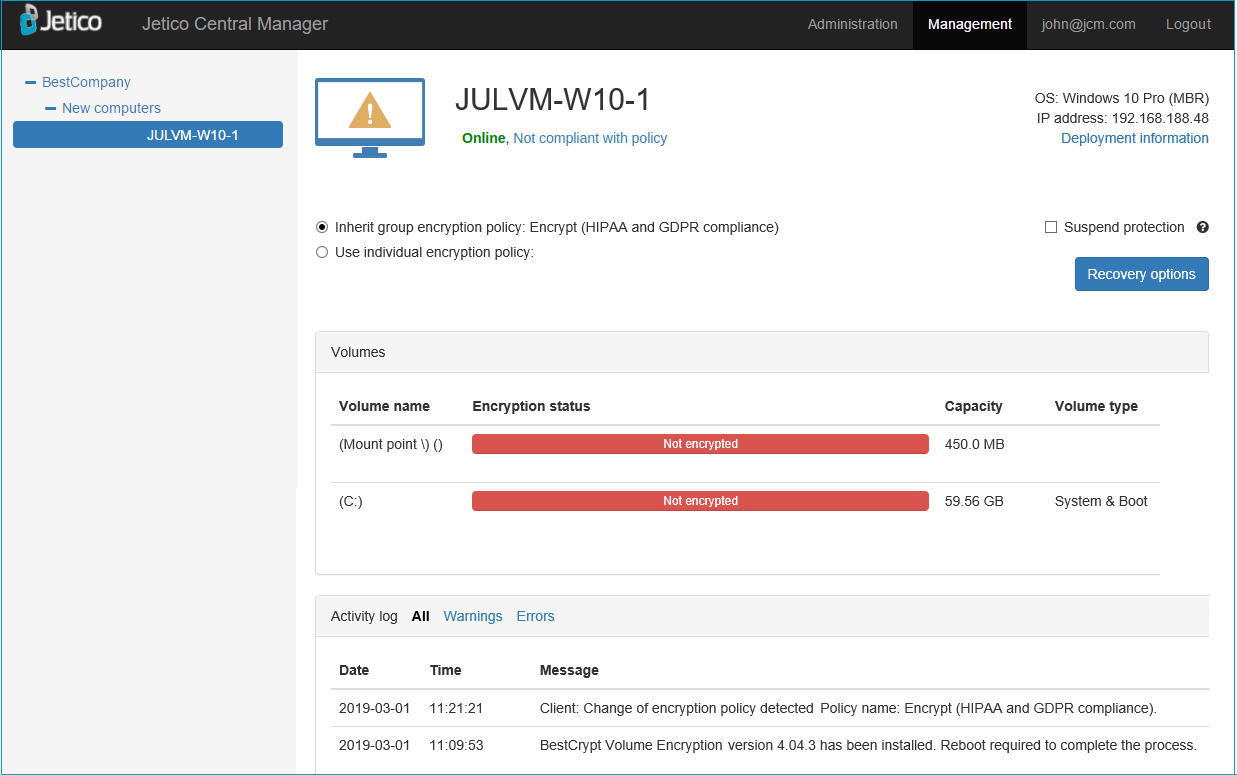
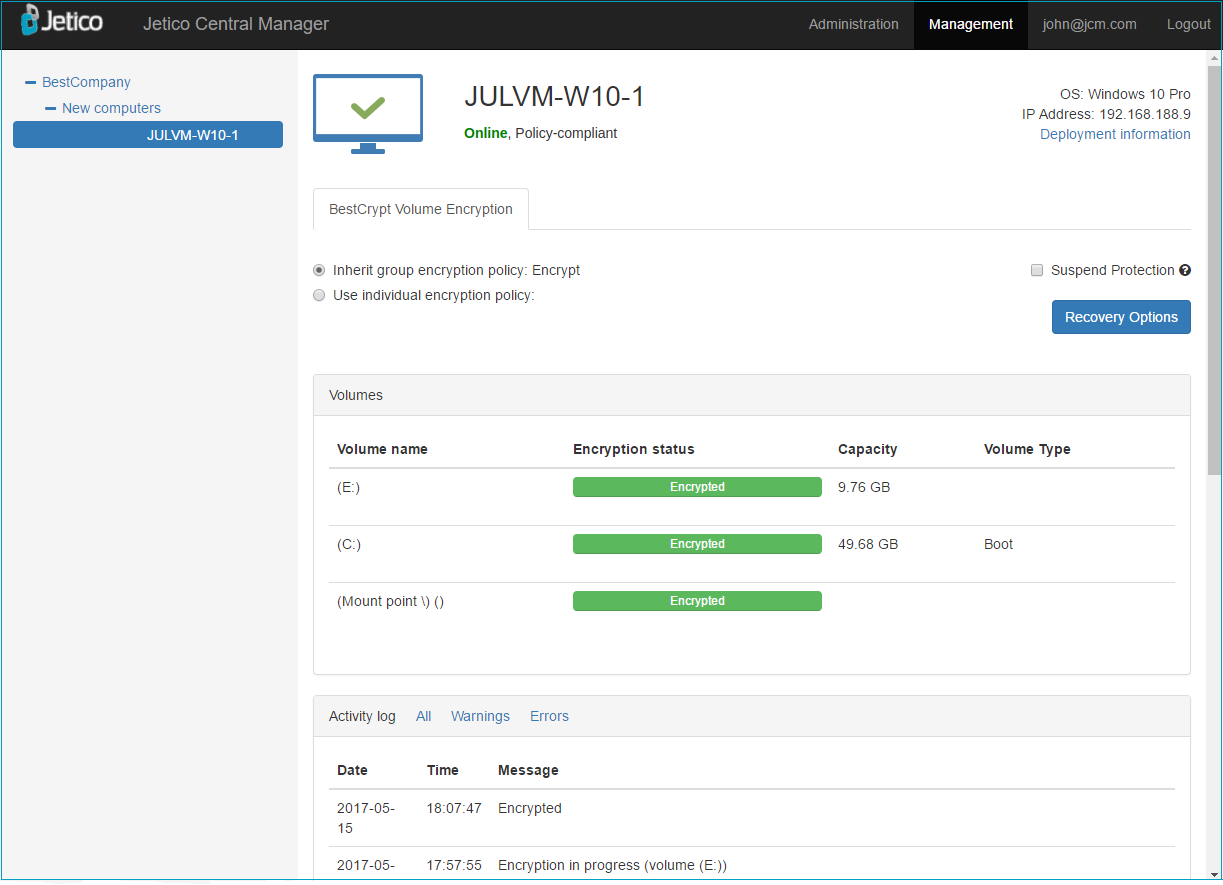
After reboot, client software will send the information about the computer (OS, IP address, volumes) to JCM server and the assigned policy will be applied:
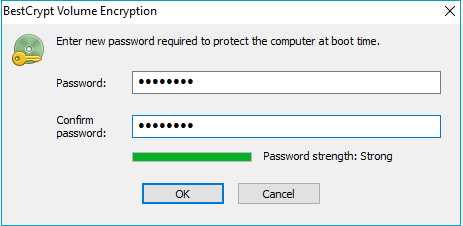
- Encrypt the computer. The program on the client computer will ask to enter the password to encrypt the computer:
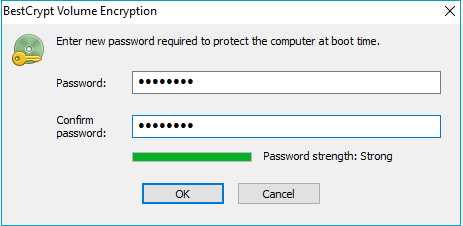
After password is entered, the encryption process will start and will be running in the background. JCM Console will show the progress.
- Process completed. When all the disks are encrypted, JCM Console will report that the computer is policy-compliant:
- Repeat steps 3 and 4 for all client computers that need to be encrypted.