BestCrypt Container Encryption software allows the user to keep any form of data (files, letters, pictures, databases) in encrypted form on the hard disk, networks disks, removable disks, CDs/DVDs and floppies. BestCrypt Container Encryption then lets you access it from any application.
BestCrypt Container Encryption allows the user to create a container file (for example, 800 Mb container file called Financials.jbc). Then the user can mount this container file as an additional logical drive: it will show up as an additional 800 Mb drive (F:\, for example). When mounted this logical drive looks and operates just like an ordinary disk drive: the user can store personal files on it. All files stored on the drive are automatically encrypted. Every read operation which addresses the drive causes decryption of the data, and every write operation causes encryption of data to be written. Using this system data is always stored in safe encrypted form and appear unencrypted only if the user enters a correct password for the container file and mounts it.
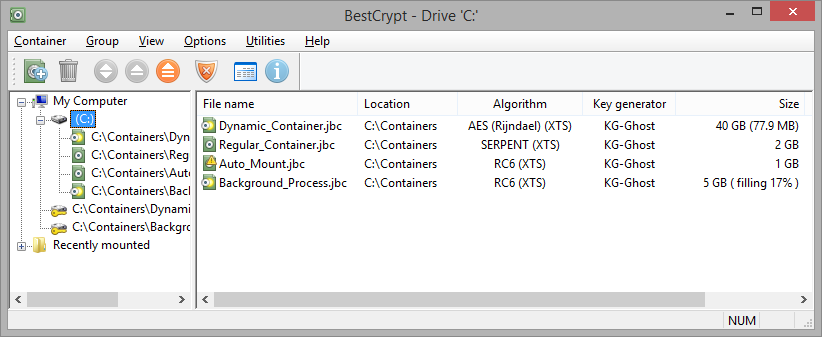
The following picture shows the BestCrypt Control Panel, which the user runs to perform all control operations like creating and mounting containers, setting BestCrypt options and so on.
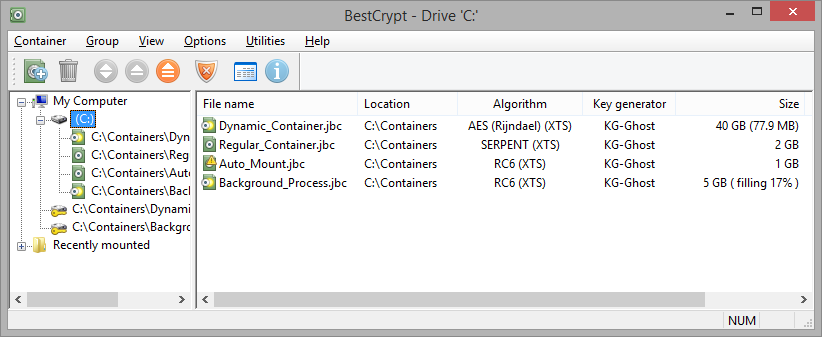
BestCrypt Container Encryption supports a number of well-known encryption algorithms (like AES, Twofish, Blowfish, CAST, GOST28147-89, IDEA, RC6, Serpent). Since BestCrypt Container Encryption uses strong encryption methods, it is practically impossible to access encrypted data without knowing a proper password or encryption key. Please read BestCrypt Container Encryption Help documentation to get more information about the functions of the software client part.
Article Central Management of BestCrypt Container Encryption in this chapter explains in more detail what kind of information Jetico Central Manager receives from BestCrypt programs running on client computers and how administrator can set recovery password for some encrypted container on client computer.