BestCrypt Volume Encryption allows the encrypting of a group of disk volumes with the same or different settings. This can be especially convenient since a user does not have to wait for the encryption of first volume to complete before starting the encryption of the second one. The software can encrypt all the volumes, each to the user’s specifications, in a single operation.
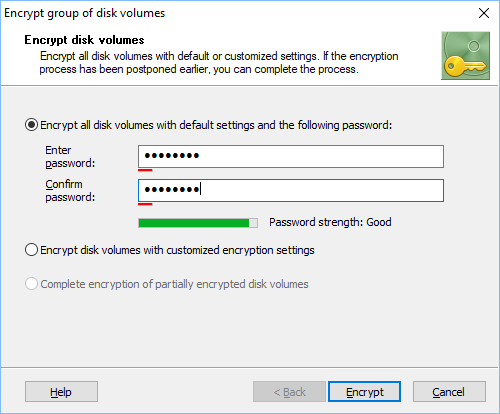
To encrypt group of volumes run the ->Encrypt group of volumes command. The following window will appear:
As the picture above illustrates, the user should choose one of the following options to proceed with encryption:
NOTE: It is not possible to encrypt removable disk drives using this command. If there are no suitable volumes to encrypt then all controls will be deactivated.
If you select Encrypt disk volumes with customized encryption settings option and click button, the following window appears.
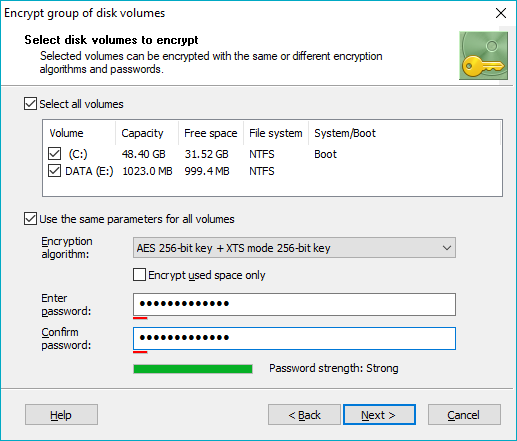
In the dialog window shown above select volumes to encrypt. If you want to use the same settings for all the volumes, check the Use the same parameters for all volumes option, choose encryption algorithm, enter password for all the volumes and click button.
If you wish to choose different settings for the volumes, remove check mark from Use the same parameters for all volumes checkbox and click button. The following dialog window will appear:
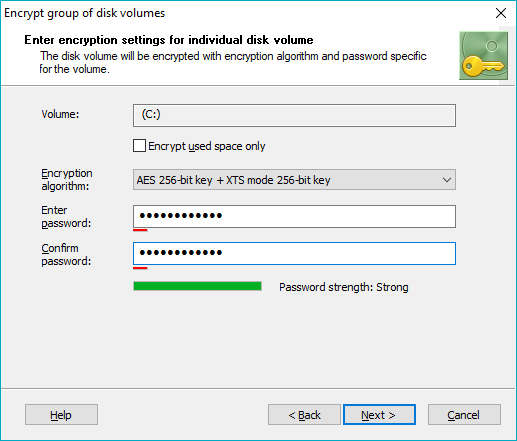
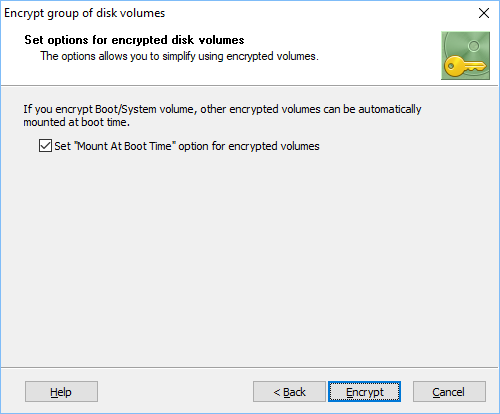
The dialog window above will appear for all volumes selected for group encryption. After entering parameters for all volumes in the group, the software will suggest you should set Mount at boot time option for the volumes. Please note that the option can be set only if you have System/Boot volume encrypted. Read more about the option in the Menu commands article.
Click button to run the process of encrypting group of volumes. As it was mentioned above, the process is time consuming and you can suspend it if needed by clicking button in the window showing the process of encryption. To continue the process run command Encrypt group of volumes again and select the option to complete encryption of partially encrypted volumes.
When you enter password for encrypted volumes, you may notice Password strength progress indicator. The software runs password strength estimation procedure based on Zxcvbn algorithm. It is recommended to choose password that would be of Good or Great strength. Read more about thealgorithm in the Security characteristics article.