In cryptography, secret sharing refers to any method for distributing a secret among a group of participants, each of which allocates a share of the secret. The secret can only be reconstructed when the shares are combined together; individual shares are of no use on their own.
The secret is opened only when specific conditions are fulfilled. Each of n participants is given a number of share, and any group of t (threshold) or more shares together can open the secret but no group of less than t shares can.
A secure secret sharing scheme distributes shares so that anyone with fewer than t shares has no more information about the secret than someone with 0 shares. Consider the naive secret sharing scheme in which the secret phrase "password" is divided into the shares "pa------," "--ss----," "----wo--," and "------rd,". A person with 0 shares knows only that the password consists of eight letters. He would have to guess the password from 268 = 208 billion possible combinations. A person with one share, however, would have to guess only the six letters from 266 = 308 million combinations. This system is not a secure secret sharing scheme, because a player with less than t shares gains significant information about the content of the secret. In a secure scheme, even a player missing only one share should still face 268 = 208 billion combinations.
Secret sharing was invented by both Adi Shamir and George Blakley independently in 1979.
Take a look at the How to use Secret Sharing Scheme video concerning the matter.
To create a new container with a secret sharing scheme, open New Container dialog and make all usual settings like name, size and location. When the Enter password dialog appears, click and choose Secret-sharing scheme in Key Block Type the edit box. The following dialog window will appear:
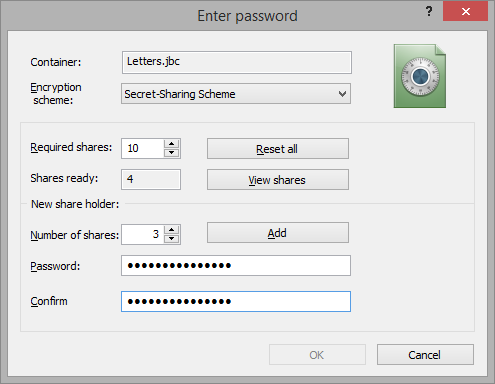
The first step is making an agreement between all the participants. You should come together and define appropriate ways of getting access to the container. You should design your secret sharing scheme based upon your needs. In terms of the scheme, you will have to define the threshold value - the number of shares required for opening the container (the value is called "Required shares" in the dialog) and number of shares for each member.
Then, each participant of the scheme will enter his/her own password and his/her own Number of shares, according to the agreement. After performing these actions and clicking the button, the password will be added to the scheme and Shares ready counter will be increased by the corresponding number of shares.
allows you to see how many passwords have already been entered and how the shares are distributed.
When the counter reaches the threshold value, will become available and creation process can be finished. But it is possible to continue the creation process, until all participants enter their passwords.
When all the participants finish entering passwords, click to continue the process of creating a new container file.