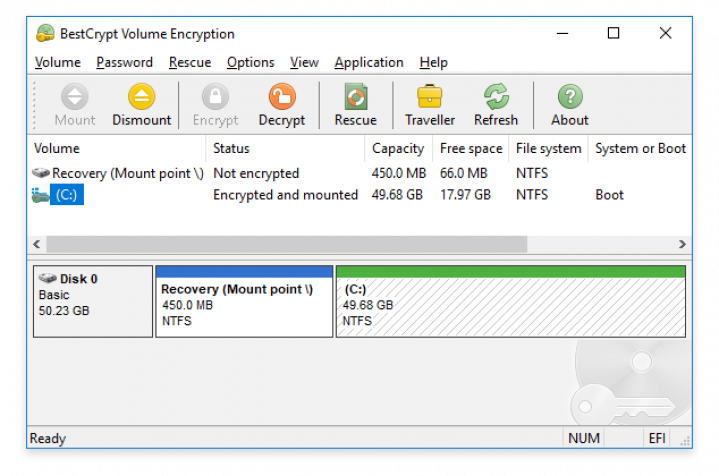
BestCrypt Volume Encryption protects all data on entire hard drives from leaking out. With Pre-Boot Authentication, BestCrypt Volume Encryption is loaded before your operating system so nobody can get access to any data on your computer or drive unless they have the right password or keys.
More and more regulations - including GDPR (see encryption requirements), NIS2, HIPAA, LGPD, SAMA and NESA - allow for exemption of data breach notification responsibilities and fines if the customer data were rendered unintelligible. Encrypting hard drives with BestCrypt Volume Encryption is an easy measure that you can take right now to comply and gain peace of mind.
Compared to full disk encryption, BestCrypt Volume Encryption offers the following added benefits:
- More flexible solution (works on RAID)
- More user-friendly method
- Lighter performance impact
Check out the 5 benefits of using volume encryption vs. disk encryption.
Since back in 2013, Jetico source code for all encryption modules (BestCrypt Development Kit) is available for download. In addition, Jetico has formally stated that BestCrypt has never included any 'backdoors' or related weakness to the software.
BestCrypt Volume Encryption is an evolved class of disk encryption products that allows users to encrypt:
- Boot/system volumes on computers with operating systems loaded according to Unified Extensible Firmware Interface (UEFI), including support for GPT partitions.
- Modern volumes residing on a number of physical disk devices, such as: Spanned, Striped, Mirrored, RAID-5 volumes
- Old MS-DOS style disk partitions
BestCrypt Volume Encryption – Enterprise Edition includes Jetico Central Manager to remotely deploy the clients across all workstations, monitor usage of encrypted disk volumes, distribute encryption policies and centrally manage recovery information necessary to access encrypted data in case of emergency. BestCrypt Volume Encryption – Enterprise Edition significantly reduces total cost of ownership, thanks to faster deployment times, minimized maintenance and superior data breach prevention.
With pre-boot authentication, BestCrypt Volume Encryption keeps your data safe while your computer is turned off. But once the ‘front gate’ is open and intruders can get inside, Volume Encryption (or any Full Disk Encryption utility) is no longer protecting your sensitive data. Mitigate these risks with BestCrypt Container Encryption and BCWipe - an active combined system of precise encryption and wiping to ensure complete endpoint data protection.
The familiar 'Volume' structure allows TrueCrypt users to encrypt hard drives the same way as always - switch to BestCrypt in a few simple steps. In addition to a painless, copy-paste migration, Jetico has published source codes to prove there are no backdoors or related vulnerabilities.